الحوسبة
تعريف التشفير القائم على الشبكة: الانعطاف بعد الكموم

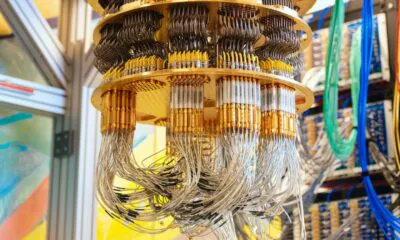
التشفير المتقدم هو نظام الأمان الخفي الذي يدعم معظم العالم الرقمي الحديث. إنها الطريقة التي تجري بها المعاملات المالية الرقمية بأمان، وكيف يمكن للجيش الحفاظ على اتصالاته مع عمليات متعددة النطاقات دون تدخل أعداء، وكيف يتم تخزين بيانات الشركات والمستهلكين بأمان. وبطبيعة الحال، إنها أيضًا أساس العملات الرقمية، كما يشير اسمها. في جوهره، التشفير هو العلوم الرياضية لتشفير البيانات القيمة بطريقة لا يمكن كسرها، بحيث يمكن فقط للمستلمين المقصودين قراءتها أو معالجتها. كما أن هذا، في جوهره، مشكلة رياضية وحسابية، فمن المنطقي أن كمبيوترًا أكثر قوة يمكنه كسر مستويات التشفير التي كانت تعتبر آمنة في السابق. هذا مشكلة خطيرة مع ظهور الكمبيوترات الكمومية، التي يُعتقد أنها أكثر كفاءة بملايين المرات من الكمبيوترات العادية لمهام معينة، بما في ذلك كسر التشفير. مع زيادة قوة الكمبيوترات الكمومية بسرعة كبيرة، هناك حاجة متزايدة إلى “تشفير ما بعد الكموم”، طرق التشفير التي تقاوم الكمبيوترات الكمومية. هذا ليس فقط قلقًا نظريًا، حيث في عام 2026، تفرض القوانين الجديدة على البنوك الأمريكية التبديل إلى نوع جديد من الرياضيات (تشفير قائم على الشبكة – LBC) لا يمكن حتى كمبيوتر كمومي فائق السرعة حله.
ميكانيكا فك التشفير الكمومي: ما وراء الحدود الكلاسيكية
خوارزمية شور ونهاية أمان RSA / ECC
الكمبيوترات الكمومية قادرة على استخدام “خوارزمية شور” لكسر مشكلة العوامل الصحيحة ومسألة اللوغاريتمات 离散 التي تُشكل أساس أمان الإنترنت الحديث. إذا بدأت الكمبيوترات الكمومية في العمل مع عدد كافٍ من الكيوبيت الوظيفية، وهو رقم يزداد بسرعة كل عام، سيكون ذلك يعني أن لا بيانات آمنة من المخترقين، ولا حساب رقمي من أي نوع. هذا مشكلة خاصة لأن الكمبيوترات الكمومية المستقبلية قد تكسر تشفير البيانات التي يتم جمعها اليوم، حتى لو كانت لا تزال لا يمكن كسرها، ولكن يمكن فك تشفيرها لاحقًا، بطريقة تسمى “الحصاد الآن، فك التشفير لاحقًا” (HNDL). لذلك، حتى لو كانت الكمبيوترات الكمومية لا تستطيع كسر التشفير اليوم، فإن بيانات اليوم بالفعل تحتاج إلى أن تكون آمنة من الكموم حتى لا تتمكن طرق HNDL من كشف كلمات المرور، والبيانات المملوكة، وسجلات طبية، وأسرار حكومية، أو معلومات حاسمة أخرى بعد بضع سنوات. سيكون هذا أيضًا يدمر على الفور كل عملة رقمية والنظام المالي ككل، حيث يمكن أن تكون المعاملات الآمنة الآن مزيفة، وجميع الأصول الموجودة في سجل رقمي معرضة للخطر، سواء في سلاسل الكتل التقليدية أو التمويل.
ما هو تشفير قائم على الشبكة (LBC)? رياضيات ل世界 ما بعد الكموم
يعتمد تشفير قائم على الشبكة على كائن رياضي يسمى الشبكة. الشبكات هي شبكات منتظمة متكررة من النقاط في مساحة مثل ورقة الرسم التي تمتد إلى الأبد، ولكنها ليست فقط ثنائية الأبعاد لأنها توجد في مئات أو آلاف من الأبعاد. الشبكة هي تشفير قائم على الشبكة للمبتدئين
تأمين التمويل الأمريكي من الكموم: التحول إلى معايير ما بعد الكموم
متطلبات 2026 PQC: متطلبات FIPS 203 و 204 و NSM-10
في عام 2024، أكملت المعهد الوطني للمعايير والتكنولوجيا (NIST) ثلاثة معايير مختلفة لتشفير ما بعد الكموم (PQC):
- FIPS 203 – ML-KEM – آلية kapsulation المفتاح القائم على تشفير الشبكة،旨 في المقام الأول كبناء أساسي للتحقق من المفاتيح الآمنة من الكموم (على سبيل المثال، في TLS أو VPNs).
- FIPS 204 – ML-DSA – نظام التوقيع الرقمي الأساسي، أيضًا قائم على الشبكة، يهدف إلى استخدامات مثل التوقيع على البرامج، والشهادات، والتحقق.
- FIPS 205 – SLH-DSA- نظام توقيع قائم على هاش بدون حالة، مبني عمدًا على افتراضات مختلفة كدعم في حالة كشف أبحاث مستقبلية عن نقاط ضعف في أنظمة قائم على الشبكة.

مصدر: NIST
“يُظهر التقدم المستمر في أبحاث الحوسبة الكمومية من قبل الأكاديمية والصناعة وبعض الحكومات أن رؤية الحوسبة الكمومية سوف تتحقق في النهاية. لذا، الآن هو الوقت المناسب للتخطيط والاستعداد والتخطيط لتحويل فعال إلى خوارزميات مقاومة للكموم، لضمان الحفاظ على أمان أنظمة الأمن القومي (NSS) والأصول المرتبطة بها.”
NSA – مجموعة خوارزميات الأمن القومي التجارية 2.0
تنفيذ PQC: الجرد والخارطة الطريقية والمرنونات الكمومية للمصارف
تترجم هذه الضغوط المتزايدة إلى متطلبات صارمة من قبل المؤسسات المالية الرائدة في الولايات المتحدة. وهذا يشمل “إظهار الاستعداد في نهاية عام 2026” عندما من المتوقع أن تكمل البنوك الأمريكية خطوتين أساسيتين:
- جرد كامل لكل مكان يستخدم فيه التشفير، مما يوفر نظرة واضحة على ما يحتاج إلى تحديث.
- خطط التحويل: خارطة طريق正式ة وموافق عليها من مجلس الإدارة لتحويل أنظمة عالية المخاطر إلى تشفير مقاوم للكموم، خاصة معايير تشفير قائم على الشبكة التي وافق عليها NIST.
- المرنونات: يتم إجبار البنوك على تبني “المرنونات الكمومية” – القدرة على استبدال خوارزمية التشفير في ليلة واحدة إذا تم كسرها فجأة من خلال اختراق كمومي.
استثمار في تشفير قائم على الشبكة
تكنولوجيا Akamai