Laskenta
Lattice-Based Cryptography: The Post-Quantum Pivot

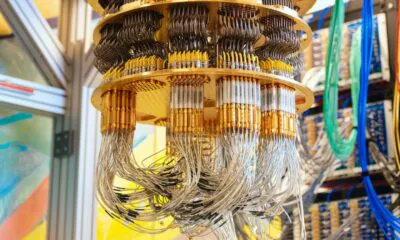
Advanced cryptography is the hidden security system supporting most of the modern digital world. It is how digital financial transactions are made secure, how the military can keep communications flowing with complex multi-domain operations and no enemy interference, and how companies’ and consumers’ data are stored safely. And of course, it is also the basis of cryptocurrencies, as their name indicates. At its core, cryptography is the mathematical science of encoding in an unbreakable manner precious data, so that only the intended recipients can read or process it. As this is, at its core, a mathematics and computation problem, it stands that a more powerful computer can break levels of encryption previously considered safe. This is a serious problem with the emergence of quantum computers, assumed to be thousands of millions of times more efficient than normal computers for certain tasks, including breaking encryption. As quantum computers are becoming increasingly more powerful at a very fast pace, there is a growing need for “post-quantum” encryption, encryption methods that are resistant to quantum computers. This is not just a theoretical concern anymore, as in 2026, new laws are forcing US banks to switch to a new type of math (Lattice-Based Cryptography – LBC) that even a super-fast Quantum computer can’t solve.
The Mechanics of Quantum Decryption: Beyond Classical Limits
Shor’s Algorithm and the End of RSA/ECC Security
Quantum computers are able to use “Shor’s Algorithm” to break the integer factorization and discrete logarithm problems that underpin modern internet security. If quantum computers start operating with enough functional qubits, a number that is rising quickly yearly, it would mean that no data is secure from hackers, nor any digital account of any sort. This is especially problematic as future quantum computers could break the encryption of data that are today collected, even if still unbreakable, but could be decoded later, a method called “Harvest Now, Decrypt Later” (HNDL). So even if quantum computers are not able to break encryption today, today’s data already needs to be quantum-proofed so that HNDL methods cannot reveal passwords, proprietary data, medical records, government secrets, or other crucial information a few years down the road. This would also instantly destroy every cryptocurrency and the financial system as a whole, as the secured transactions could now be faked, and any assets present in a digital ledger are at risk, both in blockchain and traditional finance.
What Is Lattice-Based Cryptography (LBC)? Math for a Post-Quantum World
Lattice-based cryptography leverages a mathematical object called a lattice. Lattices are regular, repeating grids of points in a space like a sheet of graph paper that goes on forever, but it’s not just 2D as it exists in hundreds or thousands of dimensions. A lattice is a
To encrypt, you start at a given grid point, move slightly away from it (adding random “noise”), and share that new location. The noise makes it nearly impossible for an attacker to determine which original grid point was used (the “right”: decrypted data), but authorized users with the “secret key” can remove the noise. The decryption with the right key is not especially computationally intensive, so it is an efficient method. But this encryption method is a form of mathematics where quantum computers have no special advantages. Traditional cryptographic methods like RSA and ECC are built on periodic structures in groups that Shor’s algorithm can solve efficiently by finding their “period”. In contrast, lattice-based cryptography does not rely on such structures.
(Further information about this technology can be found in “Lattice-Based Cryptography for Beginners“, published by the International Association for Cryptologic Research – IACR)
Quantum-Proofing US Finance: The Shift to Post-Quantum Standards
2026 PQC Mandates: FIPS 203, 204, and NSM-10 Compliance
In 2024, the National Institute of Standards and Technology (NIST) finalized three different post-quantum cryptography (PQC) standards :
- FIPS 203 – ML-KEM – A key-encapsulation mechanism (KEM) based on lattice cryptography, intended as the main building block for quantum-safe key establishment (e.g., in TLS or VPNs).
- FIPS 204 – ML-DSA – A primary digital signature scheme, also lattice-based, aimed at use cases like software signing, certificates, and authentication.
- FIPS 205 – SLH-DSA- A stateless hash-based signature scheme, deliberately built on different assumptions as a “backup” in case future research reveals weaknesses in lattice-based systems.

Source: NIST